CyberNews404 - This time found an attack called HDD Acoustic. Here the attacker can use sound waves to disrupt the normal hard drive operating mode, creating a temporary or permanent denial of state (DoS) that can be used to prevent CCTV systems from recording video recordings or freeze computers that handle critical operations.
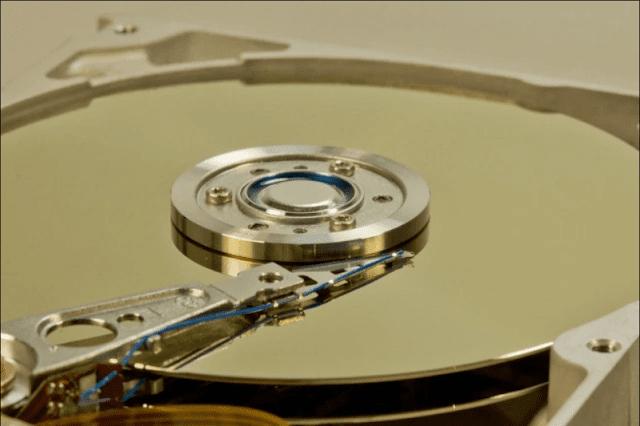
The basic principle behind this attack is that sound waves introduce mechanical vibrations to the HDD data storage plate. If the sound is played at a certain frequency, it creates a resonant effect that amplifies the vibration effect.
Because hard drives store large amounts of information inside a small area of each plate, they are programmed to stop all read / write operations during the time the dish vibrates to avoid scratching the floppy and damaging the HDD permanently.
The idea of using sounds to interfere with hard drive operations is not a new idea, previously discussed in research published almost a decade ago.
Back in 2008, Joyent CTO Brandon Gregg pointed out how loud noise caused read/write errors for the hard drive data centre, in the famous "Shouting in a datacenter" video. Earlier this year, an Argentine researcher demonstrated how he made the hard drive temporarily stop responding to OS commands by playing a 130Hz tone.
New research shows the practicality of HDD Acoustic attacks
Last week, scientists from Princeton and Purdue universities published a new study on this topic, extending previous findings with additional practical test results.
The research team used a special test rig to distinguish audio waves on hard drives from various angles, recordings to determine the sound frequency, attack time, distance from the hard drive, and the angle of the sound wave where the HDD stopped working.
Researchers have no difficulty in determining the optimum attack frequency range for the four Western Digital hard drives they use for their experiments.
They also argue that the attackers will not have any difficulty either when having to research and discover the range of attacks for HDDs they want to target.
Researchers say that an attacker who can produce acoustic signals around an HDD storage system has a simple attack place that can be used to sabotage a single company or individual.
Acoustic HDD attacks can be delivered in various ways:
Attackers can apply signals by using external speakers or exploiting speakers near the target. Towards this end, attackers have the potential to exploit remote software (for example, controlling multimedia software remotely in vehicles or personal devices), tricking users into playing dangerous sounds attached to emails or web pages, or harmful sounds in multimedia expand (for example, TV commercials).
As soon as the attacker finds a method to provide an acoustic attack, the result will vary based on a series of conditions.
For example, the closer the speakers to the hard drive, the less time it takes to perform an attack. The longer the attack progresses, the more likely that it will cause a permanent denial of service that requires the device to restart, rather than a temporary problem from which the device can recover by itself.
Furthermore, the attacker needs to pay special attention that no human operator is visible, because the attacks are in the audible range of the human ear, and the victim can investigate the origin of the monotonous sound and potentially correlate its presence with damage to local devices.
Princeton and Purdue's researchers conducted an Acoustic HDD attack on a DVR (Digital Video Recorder) device used for CCTV systems (Closed-Circuit Television), as well as on desktop computers running Windows 10, Ubuntu 16, and Fedora 27.
Attacks on CCTV systems
"After about 230 seconds of starting an acoustic attack, a pop-up warning window appears on the monitor stating that 'Disk lost!'," Says researchers about their acoustic attack on the HDD DVR.
"After stopping his voice, we tried to play back the video footage from four cameras and found that the recording had been interrupted," says the researcher. "The DVR must be restarted to fix this problem, but the video recording will be permanently lost."
Attack on the computer
The second experiment targeted desktop PCs. The researcher plays a 9.1 kHz sound frequency from a distance of 25cm to the airflow opening in this case.
"This has led to various types of malfunctions on PCs running," the research team said and revealed that they even caused a BSOD error to crash into the underlying operating system if they played their voice for longer.
Protection from an Acoustic HDD attack is required
Most of these attacks rely on playing dangerous sounds from close range. But researchers do not consider this a problem. "Using a stronger sound source can increase the range of appropriate attacks," they said.
"HDD security has been ignored despite their critical role in computing systems, HDD holds critical software components (eg, operating systems) and various forms of sensitive information (eg, camera footage in CCTV), and as such, can be an interesting thing to be an easy target for most attackers, " said the researcher.
There is the little possibility to see mass exploits of real-world devices that use acoustic attacks on hard drives, because such scenarios may not be practical because of some criteria that attackers need to be certain.
However, acoustic attacks are inherently appropriate for targeted attacks against carefully selected critical systems. For example, acoustic attacks can help state-sponsored attacks, aid with physical disturbance into secure systems, destroy or sabotage forensic collections, or even cause the loss of human life while attacking HDDs used by medical devices.
Or another example, an ATM malware gang can spread an acoustic attack to an ATM to prevent forensic evidence collection while fake malware runs on ATM RAM and handed out cash to attackers, and more.
You can learn about Acoustic HDD attacks in a research paper entitled "Acoustic Denial of Service Attacks on HDDs" by Shahrad et al.
DOWNLOAD [2.10 MB]










![[Learning Module] Metasploit The Penetration Tester's Guide : Basic Absolute For Penetration Testing](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEjgIGcys0kl5v0lguuoTfjDFY5pdnrH_-ZKRVMSCfvaZXodh3I3Y9Ketrvqw41ekC79J1tTzJ7k6zTOlRrGgh22Q4_3csCi_FPJ9_a3NV7R9q6zhKBV-mGj8NxY2wIU7FE0Gf2sdlkx95A/s72-c/Penetration-Tester-Guide-CyberNews404.PNG)

otherwise you may be subject to prosecutions under applicable laws. You should be aware that we are obliged to provide the information. Penrith CCTV
ReplyDeleteI am here to testify about how total company change my life,it was like this,i read about online trade and investment,when searching on how to trade with legit company,i ment a review which said i can invest in oil and gas company,where i can invest $5000 USD into oil and gast ,which i did after reaching total company,out end of my trade,i make a profit worth $65,0000 USD after investing with now through out thirty one days ,it real great i ment this company which change my life,i said to myself,it is better to share this on topix and forum,so that financial problem can reduce,what have your government offer to reduce financial problem,it is better you help yourself,because the system of the countries are not after our dealy bread,you can invest and get rich too,email total company at: total.company@aol.com
Delete★COMPOSITE HACKS★
ReplyDeleteAre you looking for the best Legit Professional Hackers online?
Congratulations Your search ends right here with us.
COMPOSITE HACKS is a vibrant squad of dedicated online hackers maintaining the highest standards and unparalleled professionalism in every aspect.
We Are One Of The Leading Hack Teams in The United States With So many Awards From The IT Companies. In this online world there is no Electronic Device we cannot hack. Having years of experience in serving Clients with Professional Hacking services, we have mastered them all. You might get scammed for wrong hacking services or by fake hackers on the Internet. Don't get fooled by scammers that are advertising false professional hacking services via False Testimonies, and sort of Fake Write Ups, Most Of Them are Fake Hackers/scammers and They are Always Detected Here By Signal-Arnaques.
COMPOSITE HACKS is the Answers to your prayers. We Can help you to recover the password of your email, Facebook or any other accounts, Facebook Hack, Phone Hack, you wanna monitor your kids/wife/husband/boyfriend/girlfriend, You Wanna Hack A Website or Database? You wanna Clear your Criminal Records?? Our Team accepts all types of hacking orders and delivers assured results to alleviate your agonies and anxieties. Our main areas of expertise include but is never confined to:
Website hacking, Facebook and social media hacking, Database hacking, Email hacking, Phone and Gadget Hacking, Clearing Of Criminal Records and many More
We have a trained team of seasoned professionals under various skillsets when it comes to online hacking services. Our company in fact houses a separate group of specialists who are productively focussed and established authorities in different platforms. They hail from a proven track record and have cracked even the toughest of barriers to intrude and capture or recapture all relevant data needed by our Clients.
COMPOSITE HACKS understands your requirements to hire a professional hacker and can perceive what actually threatens you and risk your business, relationships or even life. We are 100% trusted professional hacking Organization and keep your deal entirely confidential. We are aware of the hazards involved. Our team under no circumstances disclose information to any third party. The core values adhered by our firm is based on trust and faith. Our expert hacking online Organization supports you on time and reply to any query related to the unique services we offer.
COMPOSITE HACKS is available for customer care 24/7, all day and night. We understand that your requirement might be urgent so we have a separate team of allocated hackers who interact with our Clients round the clock. You are with the right people so just get started.
CONTACT US TODAY: compositehacks@gmail.com.
I am here to testify about how total company change my life,it was like this,i read about online trade and investment,when searching on how to trade with legit company,i ment a review which said i can invest in oil and gas company,where i can invest $5000 USD into oil and gast ,which i did after reaching total company,out end of my trade,i make a profit worth $65,0000 USD after investing with now through out thirty one days ,it real great i ment this company which change my life,i said to myself,it is better to share this on topix and forum,so that financial problem can reduce,what have your government offer to reduce financial problem,it is better you help yourself,because the system of the countries are not after our dealy bread,you can invest and get rich too,email total company at: total.company@aol.com
ReplyDeleteI am sure a lot of us are still not aware of the recent development of the Blank ATM card.. An ATM card that can change your financial status within few days. With this Blank ATM card, you can withdraw between $2,000-$3,000 -$5, 500-$8,800-$12, 000-$20,000-$35,000 -$50,000 daily from any ATM machine in the world. There is no risk of getting caught by any form of security if you followed the instructions properly. The Blank ATM card is also sophisticated due to the fact that the card has its own security making your transaction very safe and untraceable. i am not a stupid man that i will come out to the public and start saying what someone have not done. For more info contact Mr john and also on how you are going to get your order..
ReplyDeleteOrder yours today via Email: cryptoatmhacker@gmail.com
ReplyDeleteI'm here to testify about Mr Harry Blank ATM Cards which can withdraw money from any ATM machines around the world.. firstly I thought it was scam until I saw so many testimony about how Mr John sent them the ATM blank card and how it was used to withdraw money in any ATM machine and become rich so I decided to risk the opportunity I contacted him also and I applied for the Blank Card to my greatest surprise I have used it to get 10,000 dollars. maximum withdrawal daily $1,000, Mr Harry is giving out the card just to help the poor. Hack and take money directly from any ATM Machine Vault,If your interested kindly contact him directly on his email (harrybrownn59@gmail.com)